This week, we continue our series on Business Email Compromise. Click here to read Part 1, which includes an overview and various statistics on this growing threat.

It takes time and effort to launch a successful Business Email Compromise (BEC) attack. In a typical attack, several email messages are exchanged in an attempt to convince the target to authorize large payments to the attacker’s bank account. From start to finish, the steps involved in a BEC attack consist of identifying a target, grooming, exchanging information, and finally, transfer of funds.
Let’s go over these four steps in detail.
Step 1 – Identify the Target Victim

The first step in a BEC attack is the most research-intensive. During this step, a criminal organization profiles the target company through publicly available information found on LinkedIn, Facebook, company websites, earnings calls, podcast appearances, and conference recordings. Attackers look for the names and positions of executives or employees with access to employee records or financial data. They scour social media, online articles, and anything else that will provide specific details about the company, its vendors, its billing cycle, and its people.
What’s new in 2026 is the speed and scale of this reconnaissance. Where a single scammer once spent weeks compiling a target dossier, attackers now use large language models to scrape and summarize an executive’s online footprint in minutes — pulling in writing samples, organizational charts, vendor relationships, and travel patterns. Voice samples harvested from public speaking engagements, podcasts, and webinars are also collected at this stage; researchers have shown that as little as three seconds of clean audio is enough to clone a person’s voice. Scammers who manage to infiltrate a company’s network with malware may still spend weeks or months silently monitoring vendor invoices, payment systems, and even employee vacation schedules to time their strike for maximum effect.
Step 2 – Grooming
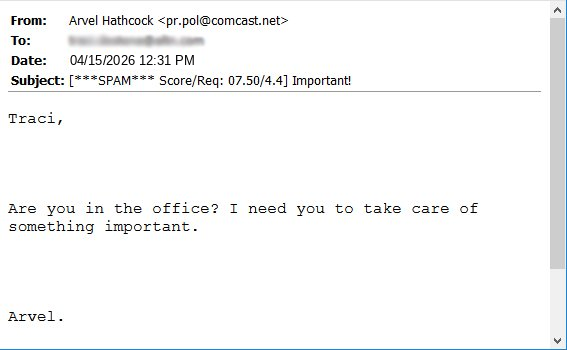
Armed with the information obtained in Step 1, the scammer moves on to the grooming phase. During this step, the scammer uses spear-phishing, phone calls, or other social engineering tactics to build rapport with employees who have access to company finances. The grooming process often takes several days of back-and-forth communication in order to build up trust. The scammer may impersonate the CEO or another executive and use his or her authority to pressure the employee to act quickly.
Here is an example of a spear-phishing email sent to one of our finance team in which the sender used display name spoofing to spoof the name of our company founder. Cybercriminals will often use a free email address (notice the free email domain), which can be easy to miss if you’re using a mobile device or a client that doesn’t display the full email header. (Note: To help the recipient identify potential phishing or spoofing, MDaemon Webmail displays the full email address taken from the message headers.)
Step 3 – Exchange of Information

Once the victim is convinced he or she is conducting a legitimate business transaction, the scammer provides instructions for transferring the funds. Traditional BEC favored international wire transfers to bank accounts in Hong Kong, the United Kingdom, China, Mexico, and the UAE — and according to the FBI’s most recent data, those corridors are still active.
What’s evolved is the destination layer. The FBI’s 2024 BEC public service announcement specifically called out a sharp rise in fraudulent funds being routed to custodial accounts at third-party payment processors, peer-to-peer payment platforms, and cryptocurrency exchanges, rather than to traditional bank accounts. ACH transfers are now also a target, alongside wires. The shift matters because cryptocurrency and P2P rails move faster and are harder to claw back than a SWIFT wire, which compresses the window for recovery from days to hours.
Step 4 – Payment

Funds are transferred and deposited into accounts controlled by the criminal organization, often passed through “money mules” who quickly move the money on to other accounts to obscure the trail. The financial damage from this final step is staggering: the FBI’s IC3 has tracked roughly $55.5 billion in global exposed BEC losses between October 2013 and December 2023. In 2025 alone, U.S. victims reported just over $3 billion in BEC losses across nearly 24,800 complaints, making BEC the second-most financially damaging cybercrime in the country, behind only investment fraud.
What to Do if You Are a Victim
If you’ve suffered losses due to Business Email Compromise, time is the single most important factor in recovery. The FBI’s Recovery Asset Team can sometimes freeze fraudulent transfers via its Financial Fraud Kill Chain process — but typically only when the incident is reported within hours, not days.
- Contact your financial institution immediately and request a recall of the funds.
- Ask your financial institution to contact the institution that received the fraudulent funds.
- Contact your local FBI field office and report the incident.
- File a complaint with the FBI’s Internet Crime Complaint Center (IC3) — and identify the incident as “BEC/EAC” so it’s routed to the right team.
You can find more detailed instructions in the FBI’s most recent Public Service Announcement on Business Email Compromise (Alert I-091124-PSA, “Business Email Compromise: The $55 Billion Scam”).
Want to learn more about how to protect yourself from Business Email Compromise scams? In Part 3, we’ll go over a few best practices, so check back soon!


