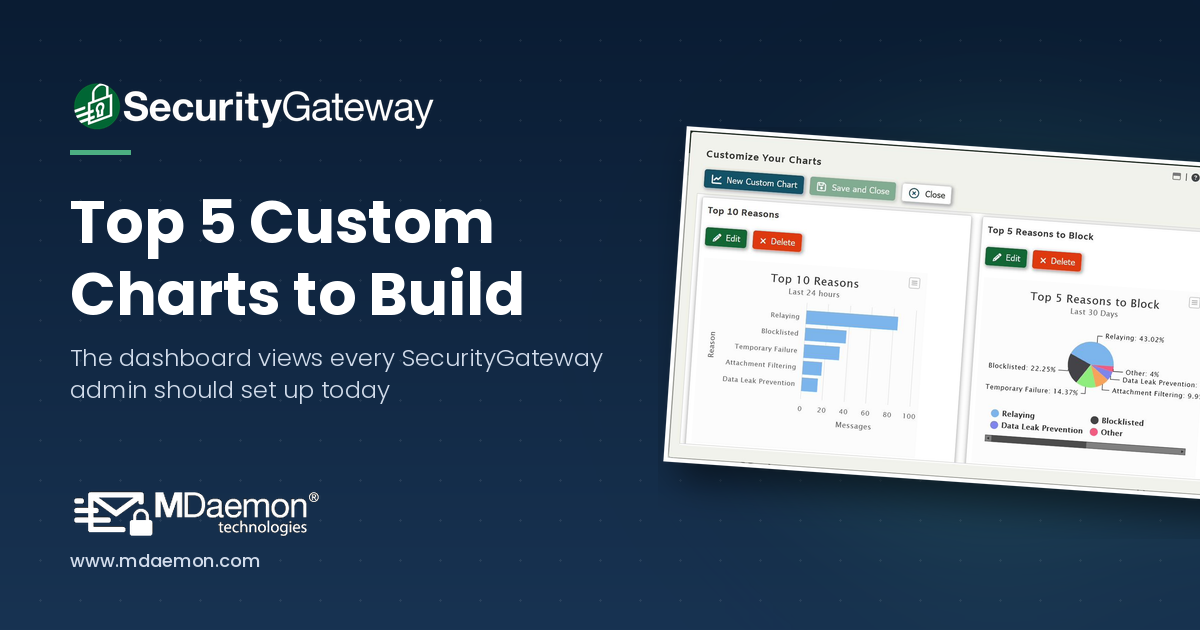
If you're an administrator using SecurityGateway for Email from MDaemon Technologies, you already know that the dashboard is your command center. It gives you an at-a-glance view of server health, message queues, spam activity, and more. But did you know you can go far beyond the default charts and build your own custom reports tailored to exactly what your organization needs to monitor?
Top 5 Most Useful Custom Charts You Can Create in SecurityGateway for Email
By Brad Wyro posted in Email Gateway How-To, Email How To, Email Security, SecurityGateway
Best Practices for Deploying MDaemon & SecurityGateway Together
By Brad Wyro posted in Email How To, MDaemon Email Server, Email Security Best Practices, Email Best Practices, SecurityGateway
Many of our customers are using both MDaemon and SecurityGateway™ together for their email security and messaging needs. Both products are loaded with anti-spam, anti-spoofing, encryption & other security features, and while some features are unique to MDaemon or SecurityGateway, many are found in both products, and therefore can be disabled in MDaemon as long as they are enabled in SecurityGateway.
How to Upgrade MDaemon Email Server (Step-by-Step Guide)
By Brad Wyro posted in Email How To, Email Best Practices, Software update, Upgrade
Running an outdated version of MDaemon Email Server can expose your organization to security risks, compatibility issues, and missed productivity features. If your MDaemon installation predates version 21, or if you’re still using a 32-bit build, now is the time to plan an upgrade.
As an IT administrator, do you find it challenging to keep up with resources and overhead as your company grows? If you use MDaemon, managing the email accounts of a growing business doesn’t have to be a time-consuming burden – because MDaemon has a feature called Account Pruning that automates the removal of inactive accounts and old email messages after a designated period of time.
How to Migrate a Single Domain From One MDaemon Email Server to Another
By Brad Wyro posted in Email How To, MDaemon Email Server
While it may be more common to move to MDaemon from Microsoft Exchange or to move MDaemon from one server to another, it's also possible to move a single domain from one MDaemon server to another - without migrating the entire server.
Improve Productivity with These Mail Server Monitoring Tools for MDaemon Administrators
By Brad Wyro posted in Email How To, Email Remote Administration, Email Security, Email Server, Email Best Practices
Email Admin Tips: How to Protect MDaemon Users from Phishing
By Brad Wyro posted in Email How To, Email Security, Phishing
Phishing continues to be a popular tactic for cybercriminals to infiltrate businesses in an effort to spread ransomware and steal sensitive data. And while the threat landscape continues to evolve, steps can be taken to help mitigate the threat of phishing attacks.
MDaemon Pro Tip: Appointment Booking using Custom Email Signatures
By Brad Wyro posted in Email How To, MDaemon Email Server, Collaboration, MDaemon Webmail
You may recall that in MDaemon 23.5, we added calendar publishing and appointment booking for MDaemon Webmail users (you can read about it here). But did you know there's an easy way to facilitate appointment booking using your email signature?
MDaemon Tech Tip: How to Hide the MDaemon Webmail Documents Folder
By Brad Wyro posted in Email How To, MDaemon Email Server, Tutorial, MDaemon Webmail
MDaemon Email Server is used by businesses in a variety of industries, including finance, manufacturing, education and healthcare, and each industry has different needs when it comes to email and collaboration. That's why we strive to make MDaemon highly customizable. One such feature is the ability to hide the Documents folder in MDaemon Webmail.
DMARC Best Practices: Securing Your Email Communications
By Brad Wyro posted in Email How To, Email Security, Anti-Spoofing, Email Spoofing, Email Security Best Practices
Discover the best practices for securing your email communications with DMARC and its importance in preventing email fraud and phishing attacks.