Recently, we published our white paper “Email Security Without Compromise – the MDaemon Approach.” In this post, we’re sharing our latest white paper, which details how SecurityGateway intercepts email threats before they reach Microsoft 365, Microsoft Exchange, or any other mail server — with multi-layered protection, deep administrative visibility, and full deployment flexibility.
Email Security at the Gateway — The SecurityGateway™ Approach
By Brad Wyro posted in Email Security, Cybersecurity, Stop Spam Email, Phishing, Email Security Best Practices, SecurityGateway, BEC
Email Security Without Compromise — The MDaemon Approach
By Brad Wyro posted in Email Authentication, Email Security, Cybersecurity, Stop Spam Email, Email Security Best Practices, Two-Factor Authentication, Email Best Practices
Our new white paper covers MDaemon's layered defense strategy, enterprise-grade security features, and why it's a compelling alternative to Microsoft Exchange and Microsoft 365.
Best Practices for Deploying MDaemon & SecurityGateway Together
By Brad Wyro posted in Email How To, MDaemon Email Server, Email Security Best Practices, Email Best Practices, SecurityGateway
Many of our customers are using both MDaemon and SecurityGateway™ together for their email security and messaging needs. Both products are loaded with anti-spam, anti-spoofing, encryption & other security features, and while some features are unique to MDaemon or SecurityGateway, many are found in both products, and therefore can be disabled in MDaemon as long as they are enabled in SecurityGateway.
AI Email Classification in SecurityGateway™ helps businesses distinguish between phishing & legitimate email
By Brad Wyro posted in Email Security, Stop Spam Email, Email Security Best Practices
SecurityGateway includes AI email classification for stronger protection against email-borne threats.
MDaemon Email Server: Security Best Practices to Protect Your Email Environment
By Brad Wyro posted in Email Security, MDaemon Email Server, Stop Spam Email, Phishing, Email Security Best Practices, Two-Factor Authentication
In an age where cyber threats are growing in both sophistication and frequency, securing your email infrastructure is more important than ever. MDaemon includes a variety of tools and settings that can help administrators protect their users and connected devices from spam, malware, hacking attempts, data breaches, and email spoofing.
Receiving Strange Emails from Yourself? Here’s What You Need to Know
By Brad Wyro posted in Email Security, Anti-Spoofing, Email Spoofing, Email Security Best Practices, Email Best Practices
It’s alarming to discover that someone is sending emails that appear to come from your email address—especially if you didn’t send them. This situation can make you wonder if your email has been hacked. However, not all suspicious activity means you’ve been compromised. In many cases, your email address may simply be spoofed, not hacked.
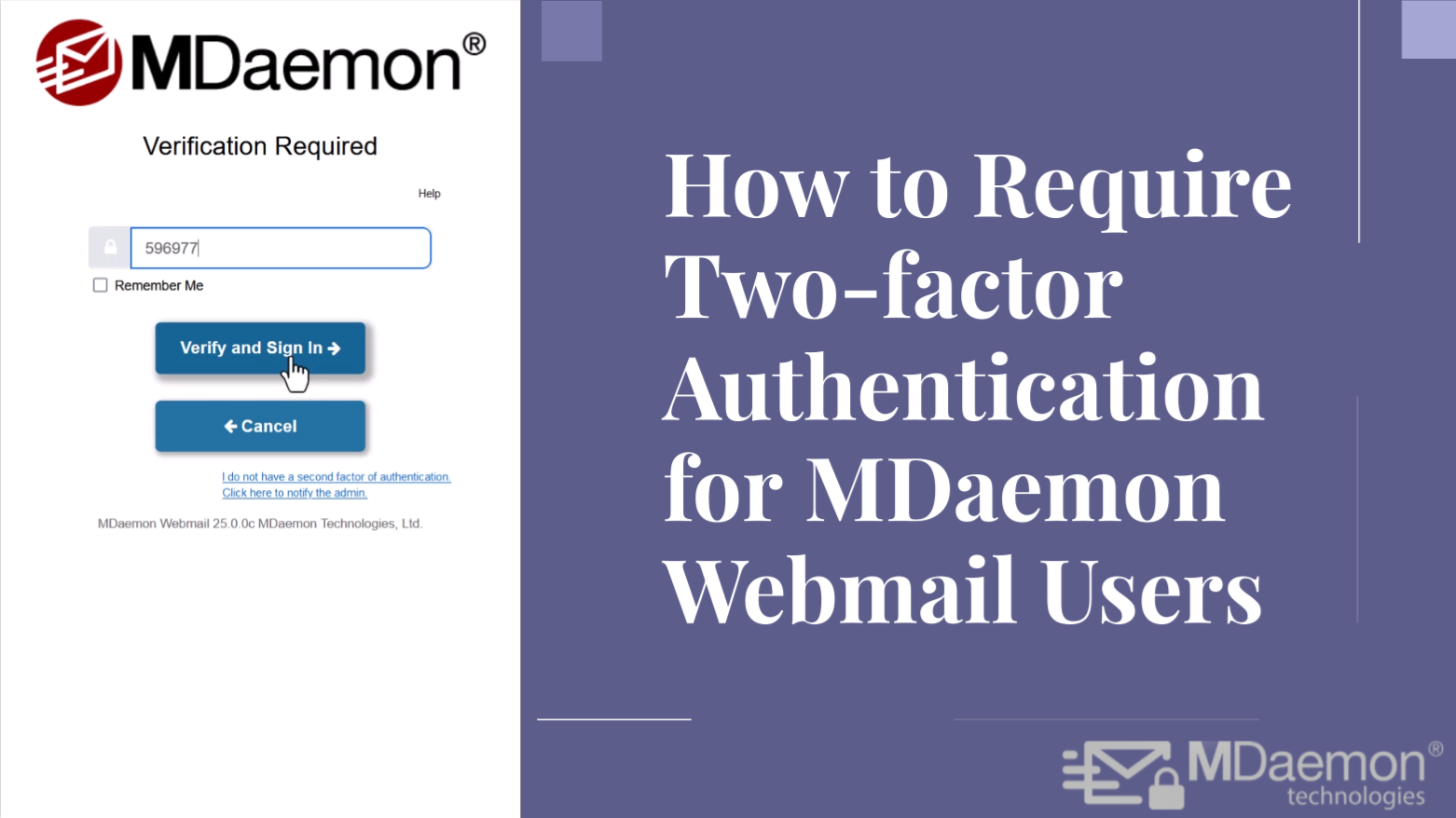
Protect Against Hackers with Two-factor Authentication for MDaemon Webmail
By Brad Wyro posted in Email Security, Email Security Best Practices, Two-Factor Authentication, MDaemon Webmail, Passwords
By now you may have heard countless stories of businesses suffering data breaches because a bad actor was able to guess a user's email password. And while I certainly recommend using strong passwords, it's more important than ever that businesses bolster their email security by requiring users to use two-factor authentication. This is especially true as even some of the strongest passwords have been exposed in hacking incidents and published on the dark web.
Email Scams to Watch Out For During the Holiday Season
By Brad Wyro posted in Cybersecurity, Phishing, Email Security Best Practices, Email Best Practices
The holiday season is a prime time for email scammers to strike. Learn how to identify and protect yourself from fraudulent emails that could ruin your festive spirit.
Watch out for election season phishing and social engineering attacks
By Brad Wyro posted in Email Security, Phishing, Email Security Best Practices, Email Best Practices
The 2024 presidential election is well under way in the United States, and that means cybercriminals are exploiting heightened public interest and uncertainty to launch targeted attacks using phishing and social engineering tactics. Here’s how they typically do it:
Protect Accounts from Hackers: 9 Tips for Stronger Passwords
By Brad Wyro posted in Cybersecurity, Email Security Best Practices, Email Best Practices, Passwords
Passwords have been the primary mechanism for online security for years, but many people continue to use poor habits when creating passwords, and this trend appears to be getting worse as the average online user has to keep track of up to 100 accounts.