
Whether you run a multi-campus medical center or a small private practice, you’ve likely heard about cyber criminals who try to trick you and your employees into clicking a link or downloading an attachment so they can steal your organization’s money or protected data.
Even if you weren’t fully aware of this before the COVID-19 pandemic, it’s crucial that you are now. These cyber criminals are exploiting widespread fear and uncertainty to target healthcare organizations of all kinds and are setting their malware to launch more quickly once inside healthcare IT networks, according to the Wall Street Journal. According to warnings from the U.S. Department of Health and Human Services, these cyberthreats range from ransomware and other types of extortion to phishing and attacks on video conferencing technology platforms. The losses can be staggering, affecting millions of patients and costing millions of dollars.
Like other businesses around the world, healthcare facilities are increasingly at risk due to the large numbers of employees accessing protected networks from home. If any point within your network becomes compromised by a successful phishing email, the attacker can gain access to a legitimate email address from which to launch other attacks. The fraudster can then lie in wait, scanning email messages for details around financial transactions or patient data, then staging a full-blown attack when sufficient information or access has been gathered.
The phishing industry is so lucrative for scammers because the barriers to entry are low relative to potential huge payouts. With botnets-for-hire and Malware as a Service (MaaS), spammers have an impressive arsenal of tools at their disposal to propagate their campaigns. Fully educating all of your network users is your best defense against phishing scams. With this in mind, here are my top 10 tips on how to identify and protect your organization from phishing attacks; make your employees aware of all of them, and reinforce this information with user training and anti-phishing drills whenever possible.
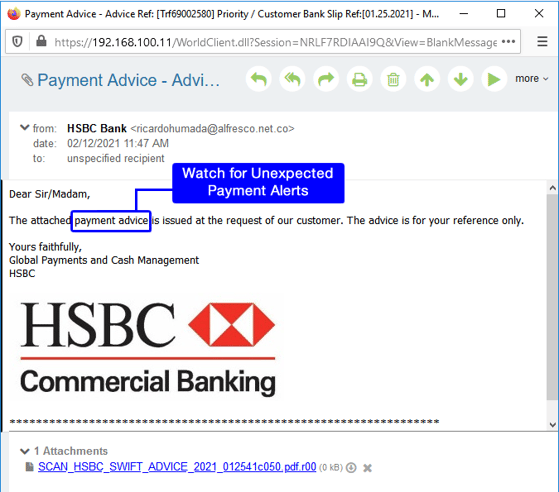
1. Watch out for messages disguised as something expected, like a shipment or payment notification. These often contain links to malware sites. Hover your mouse over any links to make sure they’re safe. Think before you click! Here’s an example using a phishing email I received claiming to come from HSBC.
2. Watch for messages asking for personal information such as account numbers, Social Security numbers, and other personal information, as legitimate companies will never ask for this information over email. Learn more about Security Gateway for Email’s Data Leak Prevention rules that prevent this type of data from being sent.
3. Beware of urgent or threatening messages claiming that your account has been suspended and prompting you to click on a link to unlock your account.
4. Check for poor grammar or spelling errors. While legitimate companies are very strict about emails they send out, phishing emails often contain poor spelling or grammar.
5. Hover before you click! Phishing emails often contain links to malware sites. Don’t trust the URL you see! Always hover your mouse over the link to view its real destination. Even if the link claims to point to a known, reputable site, it’s always safer to manually type the URL into your browser’s address bar.
6. Check the greeting – Is the message addressed to a generic recipient, such as “Valued customer” or “Sir/Madam?” If so, think twice! Legitimate businesses know and will often use your real first and last name. In our HSBC example, notice the generic greeting.
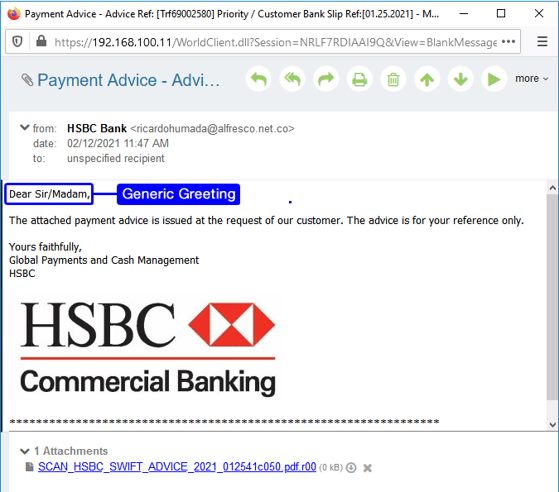
7. Check the signature block – In addition to the greeting, phishing emails often leave out important information in the signature. Legitimate businesses will always have accurate contact details in their signature block, so if a message’s signature looks incomplete or inaccurate, chances are it’s spam. In our HSBC example, the sender’s name and contact information are missing from the signature.
8. Don’t download attachments – With the proliferation of Ransomware as a Service (Raas), spammers have an easy mechanism for distributing malware-laden spam messages to thousands of users. Because the payout for ransomware can be quite high, even one successful ransomware infection could net the spammer large amounts of money. If there’s ANY doubt about the identity of the message sender or the contents of an attachment, play it safe and don’t download the attachment.
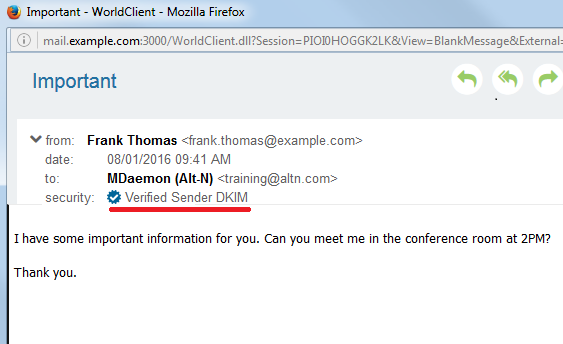
9. Don’t trust the From address – Many phishing emails will have a forged sender address. Note the From address is displayed in two places: The Envelope From is used by mail servers to generate NDR messages, while the Header From is used by the email client to display information in the From field. Both of these headers can be spoofed.
MDaemon Webmail has built-in security features to help users identify spoofed emails. For instance, many mail clients hide the From address, only showing the From name, which can be easily spoofed. In MDaemon Webmail, the From address is always displayed, giving users a clearer view into the source of the email and helping them identify spoofed senders. Using our HSBC example, I’ve highlighted the actual sender.
10. Don’t enable macros – While we’re on the subject of ransomware, another common entry point for ransomware infections is through macros in Microsoft Word documents. These documents often arrive in phishing emails claiming to have important content from HR, finance, or another important department; to trick the user, they ask the user to enable macros. Never trust an email that asks you to enable macros before downloading a Word document. If you’d prefer your users never even see such emails, Security Gateway for Email detects Word documents with macros and prevents them from being delivered.
While anti-spam and anti-malware tools can be effective at filtering out the majority of scams, tactics used by cybercriminals are constantly evolving to include heavily researched and carefully crafted messages that may contain no malware or spam-like characteristics; this means there’s really no substitute for good old-fashioned user education. Know the potential costs to your healthcare facility and don’t become the next victim!
To learn more about how Security Gateway for Email MDaemon Webmail can tighten up your email security and block phishing attacks before they reach your users, give us a call or drop us an email.


