Email is the backbone of how your organization communicates, but the server behind it shouldn't be complicated, expensive, or something you have to think about every day. That's the idea at the heart of MDaemon.
See MDaemon in Action: Watch Our Updated Overview Video
By Brad Wyro posted in MDaemon Email Server, Product Updates, Update
How to Move Your DMARC Policy from p=none to p=reject Without Breaking Mail
By Brad Wyro posted in Email How To, Anti-Spoofing, Email Security Best Practices, Email Best Practices, DMARC
This is Part 2 of a two-part series on email authentication. Part 1: Why Messages That Fail SPF, DKIM, or DMARC Still Reach Inboxes — and How to Fix It in MDaemon.
Why Messages That Fail SPF, DKIM, or DMARC Still Reach Inboxes, and How to Fix It in MDaemon
By Brad Wyro
You've configured sender authentication. You've published the right DNS records. You're checking your logs and seeing the word fail next to messages that shouldn't have been delivered, and yet they landed in user inboxes anyway.
The Envelope vs. the Letter: Why Every MDaemon Admin Should Know the Difference Between SMTP Envelope Addresses and Message Headers
By Brad Wyro posted in Email How To, Email Remote Administration, Tutorial
Most people think of an email as one thing: a message with a “From” line at the top, a “To” line right under it, a subject, and a body. Type, click send, done. That mentality works fine when everything is going right.
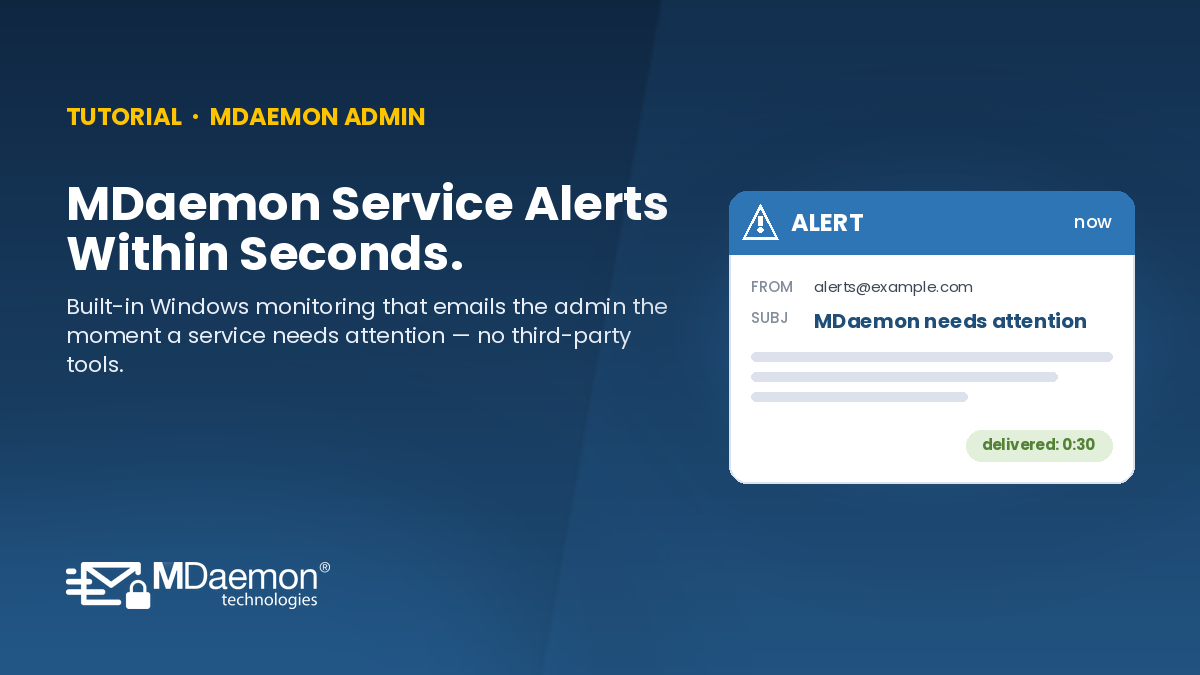
How to Use Performance Monitor to Notify an Administrator If an MDaemon Service Goes Down
By Brad Wyro posted in MDaemon Email Server, Tutorial, Email Server, SecurityGateway, MDaemon, Monitoring, Windows Server
This guide walks through the full setup end-to-end: creating the performance counter alert, adding it to a PowerShell script that sends you a notification email, and testing the whole chain so you can be confident it will work when you actually need it.
Email Security at the Gateway — The SecurityGateway™ Approach
By Brad Wyro posted in Email Security, Cybersecurity, Stop Spam Email, Phishing, Email Security Best Practices, SecurityGateway, BEC
Recently, we published our white paper “Email Security Without Compromise – the MDaemon Approach.” In this post, we’re sharing our latest white paper, which details how SecurityGateway intercepts email threats before they reach Microsoft 365, Microsoft Exchange, or any other mail server — with multi-layered protection, deep administrative visibility, and full deployment flexibility.
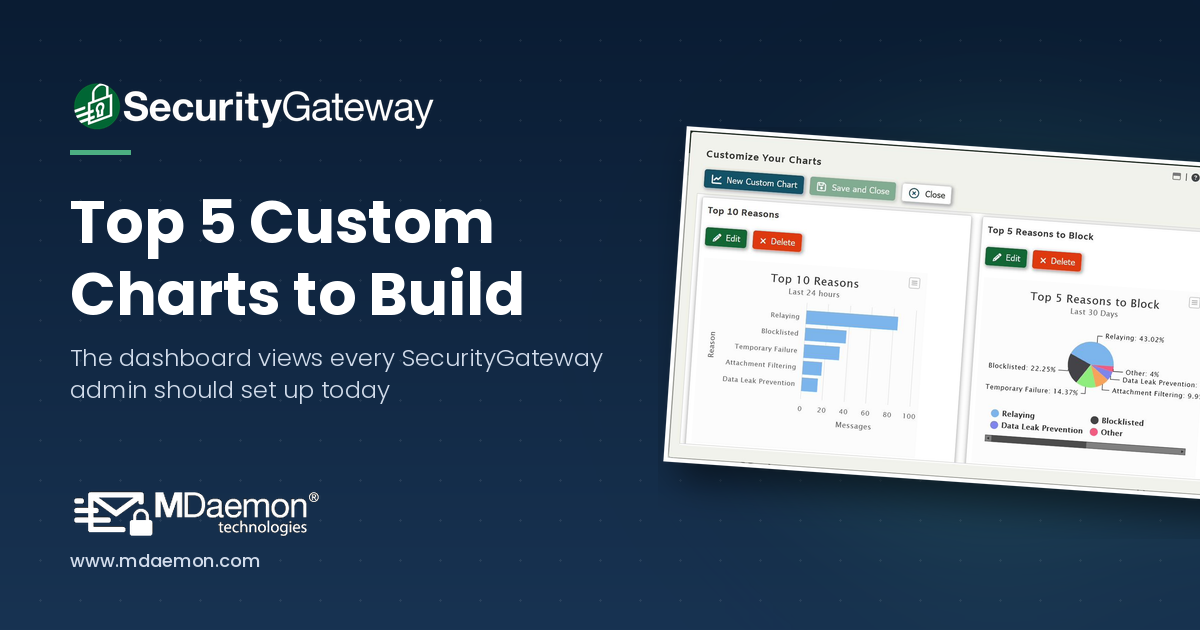
Top 5 Most Useful Custom Charts You Can Create in SecurityGateway for Email
By Brad Wyro posted in Email Gateway How-To, Email How To, Email Security, SecurityGateway
If you're an administrator using SecurityGateway for Email from MDaemon Technologies, you already know that the dashboard is your command center. It gives you an at-a-glance view of server health, message queues, spam activity, and more. But did you know you can go far beyond the default charts and build your own custom reports tailored to exactly what your organization needs to monitor?
Email Security Without Compromise — The MDaemon Approach
By Brad Wyro posted in Email Authentication, Email Security, Cybersecurity, Stop Spam Email, Email Security Best Practices, Two-Factor Authentication, Email Best Practices
Our new white paper covers MDaemon's layered defense strategy, enterprise-grade security features, and why it's a compelling alternative to Microsoft Exchange and Microsoft 365.
Best Practices for Deploying MDaemon & SecurityGateway Together
By Brad Wyro posted in Email How To, MDaemon Email Server, Email Security Best Practices, Email Best Practices, SecurityGateway
Many of our customers are using both MDaemon and SecurityGateway™ together for their email security and messaging needs. Both products are loaded with anti-spam, anti-spoofing, encryption & other security features, and while some features are unique to MDaemon or SecurityGateway, many are found in both products, and therefore can be disabled in MDaemon as long as they are enabled in SecurityGateway.
MDaemon 26 is now available - with Single Sign-on for Webmail, web conferencing improvements, and more!
By Brad Wyro posted in MDaemon Email Server, Product Updates, Software update
MDaemon version 26 is here, with improvements to web conferencing, plus Single Sign-on for MDaemon Webmail, and more!