The numbers are in, and they paint a troubling picture for the healthcare industry.
Why healthcare organizations must strengthen their email security
By Brad Wyro posted in Email Security, Security Gateway for Email, Health Care Security, SecurityGateway
Why Automating TLS Certificate Renewals Is More Important Than Ever
By Brad Wyro posted in Email Security, Encrypt, Email Encryption, Cybersecurity, ssl, SecurityGateway
TLS (Transport Layer Security) is a cryptographic protocol that allows secure communication over a network. It uses a certificate issued by a trusted CA (certificate authority) to encrypt connections between clients and servers. These certificates must be renewed periodically to ensure continued data privacy.
Receiving Strange Emails from Yourself? Here’s What You Need to Know
By Brad Wyro posted in Email Security, Anti-Spoofing, Email Spoofing, Email Security Best Practices, Email Best Practices
It’s alarming to discover that someone is sending emails that appear to come from your email address—especially if you didn’t send them. This situation can make you wonder if your email has been hacked. However, not all suspicious activity means you’ve been compromised. In many cases, your email address may simply be spoofed, not hacked.
Email Admin Tips: How to Protect MDaemon Users from Phishing
By Brad Wyro posted in Email How To, Email Security, Phishing
Phishing continues to be a popular tactic for cybercriminals to infiltrate businesses in an effort to spread ransomware and steal sensitive data. And while the threat landscape continues to evolve, steps can be taken to help mitigate the threat of phishing attacks.
Want to become an MDaemon guru? Watch our technical training webinar!
By Brad Wyro posted in Email Security, MDaemon Email Server, Training
Are you an MDaemon administrator needing some help understanding certain features? Looking for email troubleshooting tips & tricks? Well look no further than our MDaemon Technical Training webinar!
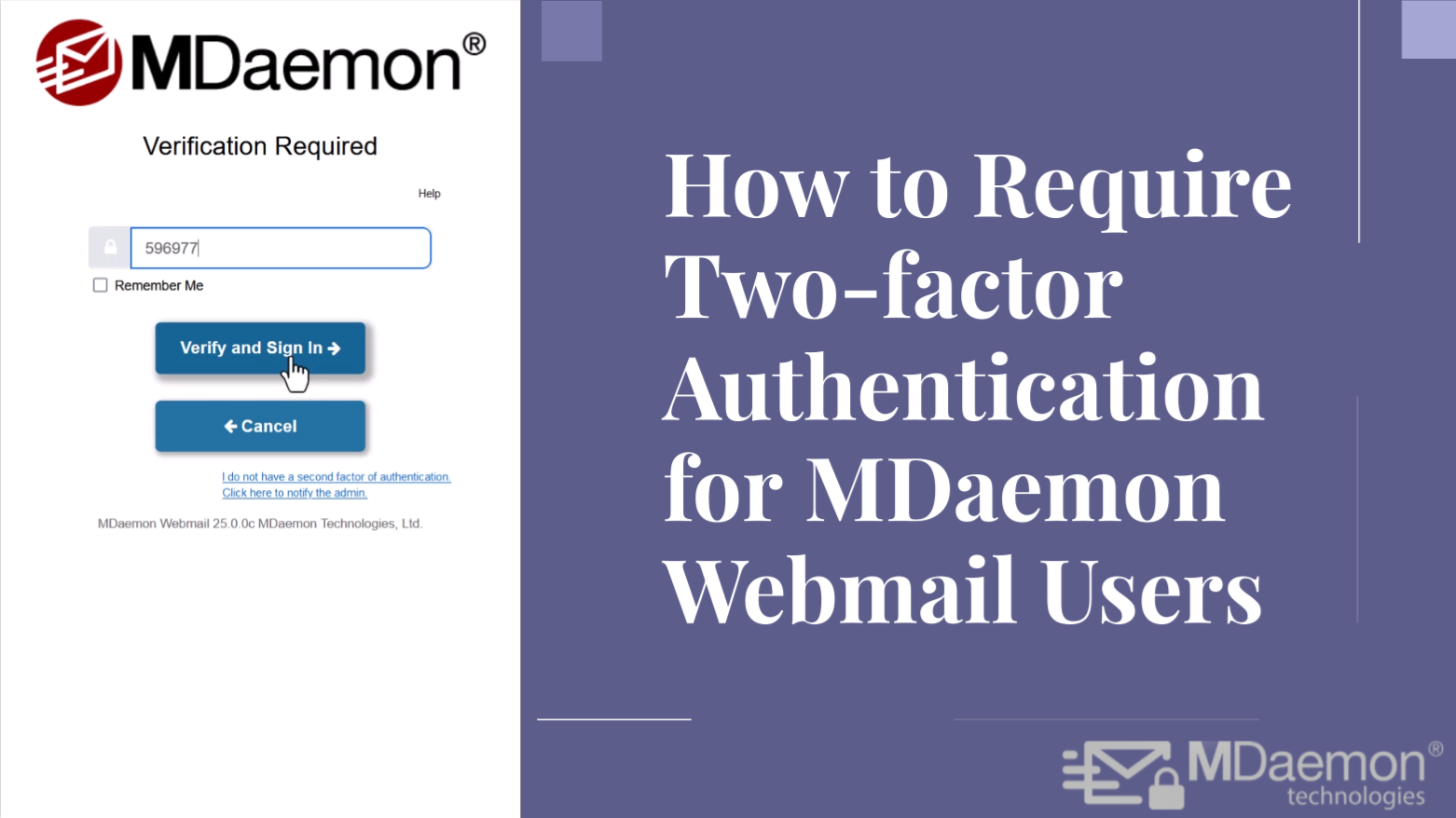
Protect Against Hackers with Two-factor Authentication for MDaemon Webmail
By Brad Wyro posted in Email Security, Email Security Best Practices, Two-Factor Authentication, MDaemon Webmail, Passwords
By now you may have heard countless stories of businesses suffering data breaches because a bad actor was able to guess a user's email password. And while I certainly recommend using strong passwords, it's more important than ever that businesses bolster their email security by requiring users to use two-factor authentication. This is especially true as even some of the strongest passwords have been exposed in hacking incidents and published on the dark web.
Watch out for election season phishing and social engineering attacks
By Brad Wyro posted in Email Security, Phishing, Email Security Best Practices, Email Best Practices
The 2024 presidential election is well under way in the United States, and that means cybercriminals are exploiting heightened public interest and uncertainty to launch targeted attacks using phishing and social engineering tactics. Here’s how they typically do it:
How to Block Executable Files in SecurityGateway™ for Email
By Brad Wyro posted in Attachments, Email Security, Anti-Virus
Malware can be delivered in many ways - via hyperlinks pointing to malicious websites, Microsoft Word documents containing malicious macros, or un-patched software. Or a bad actor can simply add a malicious file as an attachment to an email message and use social engineering to try to trick the user into clicking on the file.
Stay One Step Ahead: Anti-Phishing Best Practices for Your Business
By Brad Wyro posted in Email Security, Phishing, Email Security Best Practices, Email Best Practices
Protect your business from phishing attacks with these essential best practices. Stay one step ahead of cybercriminals and safeguard your sensitive data.
Discover the latest technique cybercriminals use to deceive victims and gain unauthorized access to sensitive information.